However, because it is of vital importance, the IT team needs the necessary tools. We are not supposed to act only “fighting fires”. In this manner, it will be necessary to have the capacity of anticipating to the problems. Mainly, in relation to addressing the visibility of the network. The analysis of the network behavior is crucial for the detection of abnormalities, configurations of validation and resource reallocation.
ALTERATION OF THE NETWORK BEHAVIOR
We know that in terms of information technology the changes are continuous. And the applications are constantly updated. As well as, new technologies are launched. With that, the behavior of the application in the network also can be changed. The traffic that was generated normally by such application can be changing gradually. What if the performance of this or the other applications could be damaged?
In another scenario, new devices are being connected to the network, such as, for example, wireless devices. All of those new devices are being gradually connected to the network. In this manner, adding a new volume of traffic. Will the addition of that new equipment represent a significant change in the current traffic?
We could even, approach situations where the applications that shouldn’t be trafficking in the network, start occupying a relevant percentage of the traffic. Namely due to the misuse of the computational resources or by some user, or even coming from the propagation of some malware. Even if it is gradual, such as identifying that alteration in the traffic?
ALARMS OF ALTERATION OF BEHAVIOR
In order to obtain a better understanding about the behavior of the network, we should not remain restricted only to the scalable features. That is to say, beyond analyzing the defined limits in an explicit manner, we also want to verify all the typical behavior of the application. So we won’t be restricted to the analysis of only one static peak of traffic. Therefore, we are able to accompany the behavior of the usage of network resources, as well as identifying potential problems.
In order for this follow-up to happen, the TRAFip counts with alarms of behavioral change. Where from a daily basis, the system will compare the metric collected with the expected chart. The alarm will be activated in case the collected metric differs from the expected value plus the tolerance defined by the user. Namely, if the average traffic violates the maximum and minimum limits expected, the alarm will be triggered.
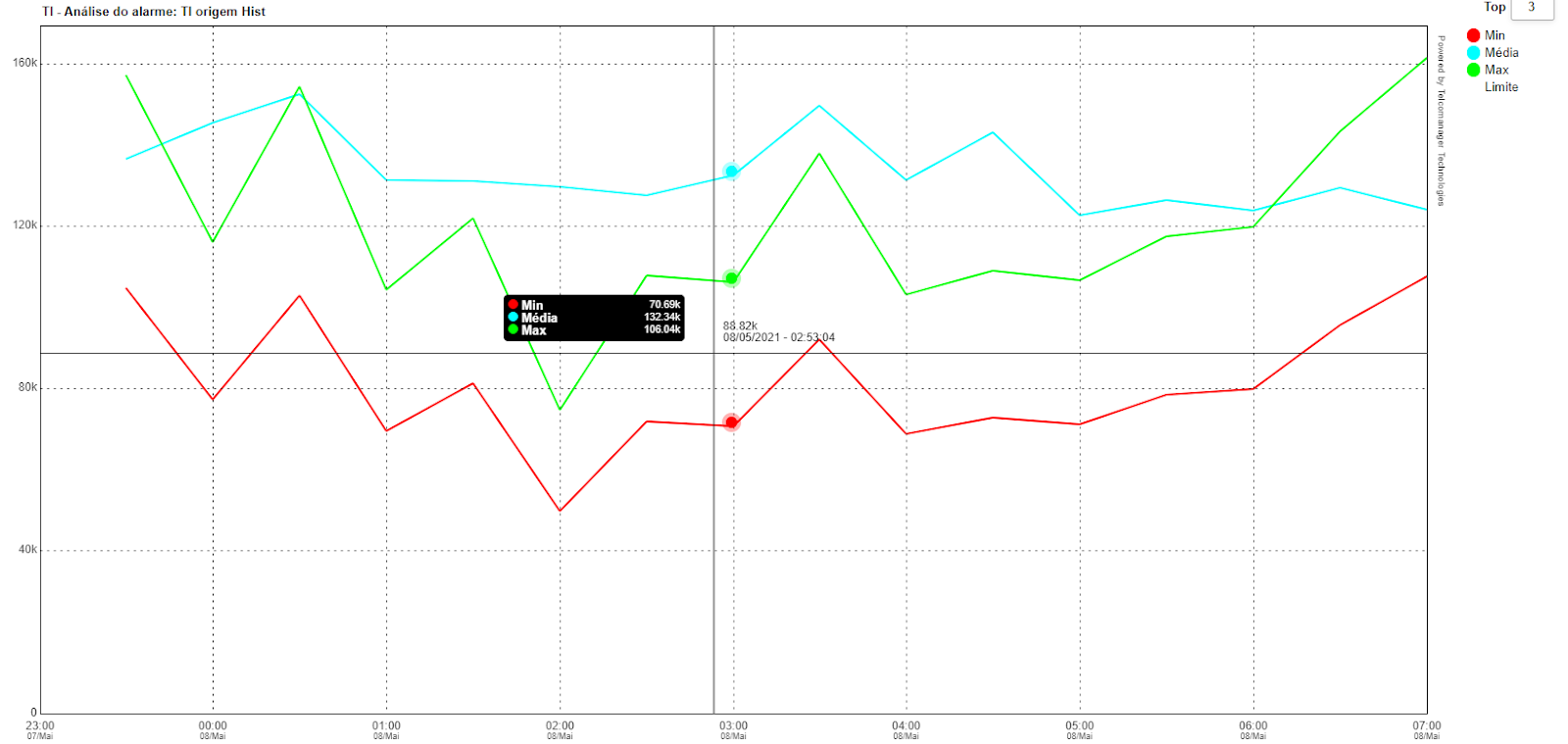
The alarm configuration in the alteration of behavior, on the TRAFip, is extremely flexible. The administrator will be capable of defining the size of the historical basis for the mounting of the expected chart. As well as defining the violation rules for the behavioral change to be computed. In relation to the activation conditions, the administrator will be able to define protection values, in order to avoid unnecessary alarms and if desirable to be notified about the traffic, above, below or both in reference to the expected traffic.
FINAL CONSIDERATIONS
Alarms and notifications, keep the IT team informed about any alteration relevant to the network. Thus, guaranteeing a more efficient and proactive IT. The notifications in the TRAFip will be able to be sent by e-mail, SMS, telegram, trap or even activating a personalized script.
In this sense, there is no doubts about the importance of having investments in network management. Bringing therefore not only benefits to the visibility of networks but also being a way to guarantee greater governance.
Thinking of that, Telcomanager present in the market since 2002, and a leading Latin America brand in the sector of software for managing networks. Also counting with a unique and innovative technology, deploying smart solutions in the monitoring of data that will provide a stratified vision of the traffic, is now allowing your Company to follow the most important aspects of your network, in real time.
 +55 (21) 3211-2223 info@telcomanager.com
+55 (21) 3211-2223 info@telcomanager.com